Let Us Manage Your Cloud Security
 Cloud Security Services
Cloud Security Services
Many businesses and government agencies migrating to cloud services because of the collaborative capabilities, flexibility, and overall lower costs. One of the other top reasons these organizations are moving to the cloud is because of the premium security features they provide with much more capability than what can be done on-premises. But doesn’t that make cloud services a large target for malicious attackers?
The answer is yes and the cloud providers know that. Microsoft is often called the largest telemetry network in the world with billions of devices handling billions of authentications every month and scanning over 400 billion emails a month. When Artificial Intelligence is introduced, new attack vectors are identified.
The result of this global telemetry and analysis is a next generation of security products – available to you as a cloud services subscriber.
Evaluate Your Cloud Security Posture
Even while utilizing the cloud as the most secure infrastructure available for your business there are still recommended security practices that must be followed. Consider the security settings of your cloud tenant, security of your organization’s network, and security for traveling users. All of these areas present opportunities for attackers. You need to ask, is your team proficient in all of the latest security threats or do they need help?
 Managed Cloud Security Services
Managed Cloud Security Services
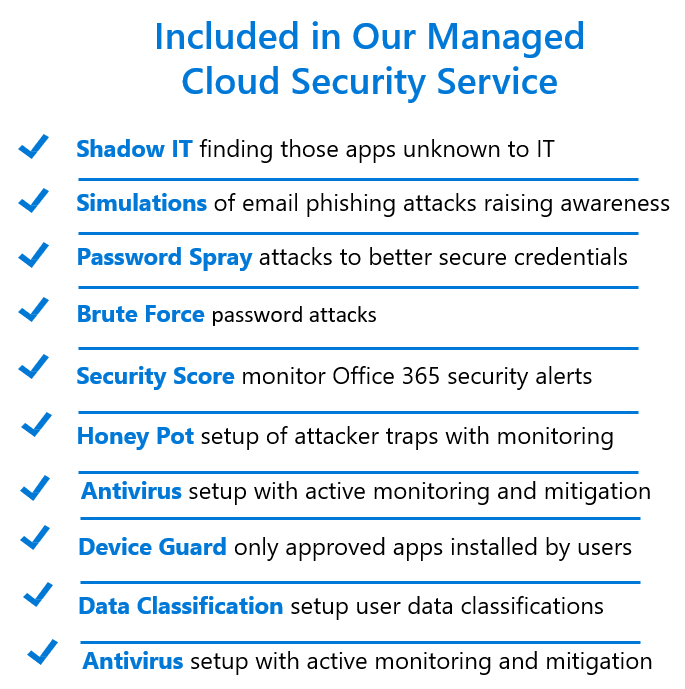
After many years of customer engagements and hearing concerns about security both on-premises and in the cloud, we are now offering a security service as part of a managed solution. We have an experienced team of security focused engineers available to become your organization’s technical security department at a very low cost. Put your security concerns to rest by trusting our team. We offer all of the services above as part of our managed cloud security service. Additional service information is available on the back of this document.
 Shadow IT Monitoring
Shadow IT Monitoring
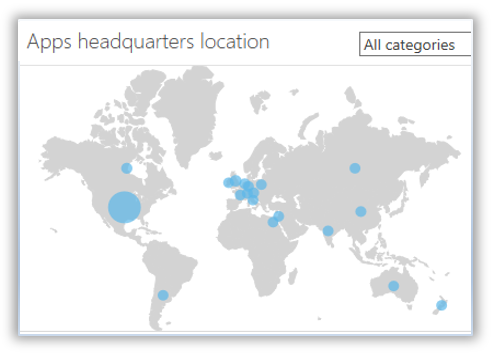
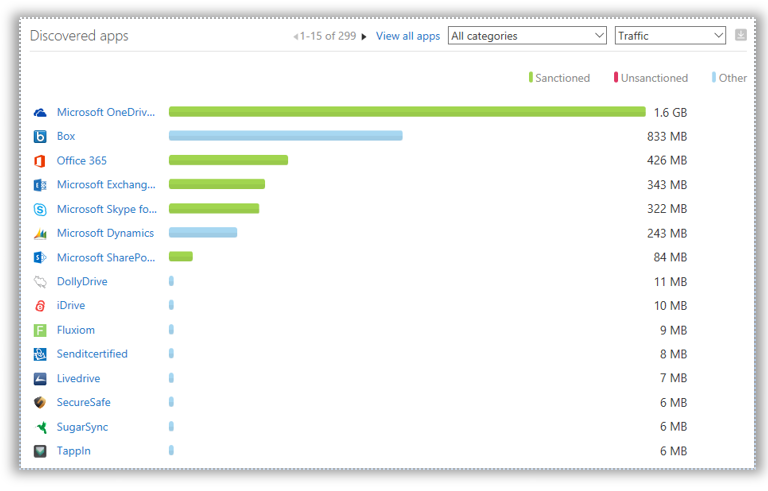
While an organization’s technical department provides the tools needed for productivity, many organizations are now concerned about applications and tools they are not aware of. These applications are seen by users and randomly installed, sometimes going viral before a technical department is aware of its existence. While users may consider these new tools to be “cool,” they represent very real dangers to an organization’s data security and potential network breaches.
Our managed security service will continuously monitor for these unsanctioned applications known as Shadow IT.
Azure Sentinel Deployment
Through SIEM deployments, an information security team can manage an organization’s cyber defense operations from a single focal point. With the release of Microsoft Azure Sentinel SIEM, as a native cloud service, the effort to deploy and configure the SIEM has been significantly reduced, and so have costs and time.
Trifecta Cloud Security Solutions can help your organization to get the your Azure Sentinel instance up and running quickly. We know all typical SIEM deployment challenges and our experts in Azure Sentinel have done numerous successful installations for businesses of various sizes.
As part of our Azure Sentinel SIEM deployment, Trifecta will:
- Asses your existing infrastructure to understand your SIEM needs
- Provide an initial SIEM infrastructure design matching your environment
- Configure Azure Sentinel to work alongside your current SIEM solution (if needed)
- Educate you on projected Azure consumption for the final SIEM solution
- Build and configure Azure Sentinel cloud instance in your Azure tenantID
- Review log types and devices, both on-premises and in Cloud and educate you on relevant log sources to be included in SIEM analytics
- Assist you with the on-premises log sources on-boarding activities
- Create a set of Sentinel alert rules and playbooks matching your needs and remediation capabilities
- Complete initial tuning of alert rules
- Create custom workbooks/dashboards for both security and operational teams
- Perform knowledge transfer and Sentinel platform training for your SOC team
- Optionally, you may opt to use the Managed Sentinel Agent for centralized log collection, parsing and indexing
Azure Sentinel Management
STARTER SIEM PACKAGE
Our starting SIEM package is the ideal cost efficient package for small to medium size organizations. This service is limited to the core log sources and provides more automation with customer tools. We made this service as a perfect start for SMB organizations which, until now, could not afford to manage or outsource a SIEM service.
ENTERPRISE SIEM PACKAGE
Our full SIEM package is ideal for Enterprise level organizations, as an end-to-end SIEM service running on Azure Sentinel platform. Part of the service, the proprietary Managed Sentinel Log Collection agent will be deploy on-premises in order to optimize the Azure log consumption. Additionally the service will be enriched with external Threat Intelligence feeds to help mitigate your organization’s risk, lower your response times, and maximize your security investment allocations.
Both Managed Sentinel Inc. SIEM services will provide:
- Continuous fine-tuning of Sentinel alerts and playbooks
- Advanced monitoring of availability and capacity of all log sources (cloud or on-premises)
- Integration with your ticketing systems (if supported)
- Regular alerts and monitoring of Azure cloud consumption and costs
- Monthly service review
- Adhoc IoC (indicator-of-compromise) searches in Azure Sentinel logs on your request
- Custom dashboards with relevant customer information for both security and operational aspects
- Threat Intelligence feeds integration
- Service support and assistance during alert triage and escalation
- Deployment and management of proprietary Managed Sentinel log collection agent deployed on your premises.
 Microsoft Office 365 Security Monitoring
Microsoft Office 365 Security Monitoring
Securing your Microsoft Office 365 cloud environment and network is critical to your overall security posture. Our team of security experts will help ensure that your company’s critical data is protected. Our monitoring activities leverage a set of clear, proven processes and recommendations, leveraging Microsoft’s Office 365 Security Assessment.
While security provided by cloud vendors is by far the safest environment to use today for your organization, how each of the settings are defined must continuously be evaluated. Any changes to your security posture will trigger an alert to us.


